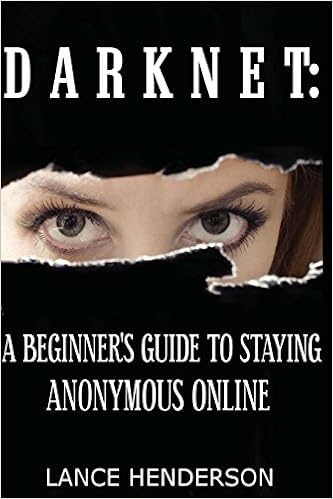
Darknet: A Beginner's Guide to Staying Anonymous Online
Lance Henderson
Language: English
Pages: 88
ISBN: 1481931385
Format: PDF / Kindle (mobi) / ePub
Want to surf the web anonymously? This book is the perfect guide for anyone who wants to cloak their online activities. Whether you're on Usenet, Facebook, P2P, or browsing the web with standard browsers like Opera, Firefox and Internet Explorer, I will show you how to become a ghost on the internet, leaving no tracks back to your isp, or anyone else. This book covers every facet of encrypting your private data, securing your pc, masking your online footsteps, and gives you peace of mind with TOTAL 100% ANONYMITY on the internet. - Learn how to mask your online identity with *every* site or protocol you use online - In depth guides on Tor, Freenet, I2P, Proxies, VPNs, Usenet and much, much, more! - Learn about basic mistakes that even advanced hackers make every day that give them away - Learn which programs make you a ghost on the internet, and which shine the spotlight on you! - Get 100% security with online *and* offline computer habits! Regardless of what you do online, you owe it to yourself to make sure you aren't taken advantage of!
IPv6 Fundamentals: A Straightforward Approach to Understanding IPv6 (Fundamentals Series)
Excel VBA Programming For Dummies (3rd Edition)
But How Do It Know? - The Basic Principles of Computers for Everyone
Tracking system developed by Norway’s National Criminal Investigation Service. It tracks peer-to-peer identities (ip addresses) on the Emule network, and monitors illegal files being traded over the network. It can detect such files based on their SHA value, the digital fingerprint that a file possesses. All types of files have this digital fingerprint: mp3s, divx video files, text files, you name it. If any part of the file is altered, say with a paint program for jpegs, then the SHA value.
Right to your very doorstep. With the help of Google Maps, and a whole plethora of other mapping applications, this can potentially lead to some very annoying and/or embarrassing situations. Do you think this information would be valuable to door-to-door salesmen? Or perhaps a company that sends out mailed advertisements? Of course it would! First things first, let’s briefly say a word about the difference between privacy and anonymity. They are not the same thing. Not by a long shot. Privacy.
And Anonymity While we shouldn’t waste time splitting hairs here, it is probably a good idea to distinguish between the terms “privacy” and “anonymity”. The two terms are not really as interchangeable as some think. Let’s say that you have Firefox running, and you are working from home with a direct connection to your ISP. You don’t want anyone knowing what you’re doing, so you select the “private mode” tab in Firefox. This disables cookies and inhibits the ability to store any remembered.
Involved with torrenting, and will send your real IP address to the tracker, thereby defeating the purpose of using Tor completely. Tor in fact still does what it is coded to do: send whatever packets anonymously through the Tor network to your destination. However it sends your IP address within the torrent tracker right along with it…anonymously. It would be like sending a secret message in an envelope directly to the person you are attempting to hide that message from. This is not a problem.
Mini-snapshot of the pictures unless this is disabled. Windows 7 is a completely different file system to Windows XP. Instead of keeping the thumbnail cache within the folder where the pictures reside, it stores it in a central location (%userprofile%\AppData\Local\Microsoft\Windows\Explorer) I have found it much better to just leave the thumbnail option off in Windows 7, as the images load fairly quickly without the need for a cache to speed things up. There are other files, like text, audio.
